JWTs Explained: A Comprehensive Guide for Secure API Authentication
In the ever-evolving landscape of web development, securing APIs and managing user sessions efficiently are paramount. Traditional session-based authentication, while robust, often introduces complexities, especially in distributed systems, microservices architectures, and mobile applications. This is where JSON Web Tokens (JWTs) step in as a powerful, stateless, and widely adopted solution.
Are you tired of managing complex session stores or dealing with cross-domain authentication challenges? Do you want a more scalable and efficient way to handle user identity and authorization across your services? If so, understanding JWTs isn't just beneficial – it's essential. This comprehensive guide will demystify JWTs, breaking down their structure, explaining their operational flow, exploring their real-world applications, and arming you with the knowledge to implement them securely in your projects.
Let's embark on a journey to unlock the full potential of JWTs and elevate your application's security and scalability.
What Exactly are JSON Web Tokens (JWTs)?
At its core, a JSON Web Token (pronounced 'jot') is a compact, URL-safe means of representing claims to be transferred between two parties. These claims are pieces of information regarding an entity (typically, a user) and additional metadata. The beauty of JWTs lies in their ability to be self-contained: they carry all the necessary information within themselves, making them ideal for stateless authentication and authorization mechanisms.
Unlike traditional session IDs that reference server-side session data, a JWT itself contains the user's identity and permissions, signed to prevent tampering. This means a server doesn't need to query a database for every request to verify a user's identity; it can simply validate the token.
JWTs are an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed.
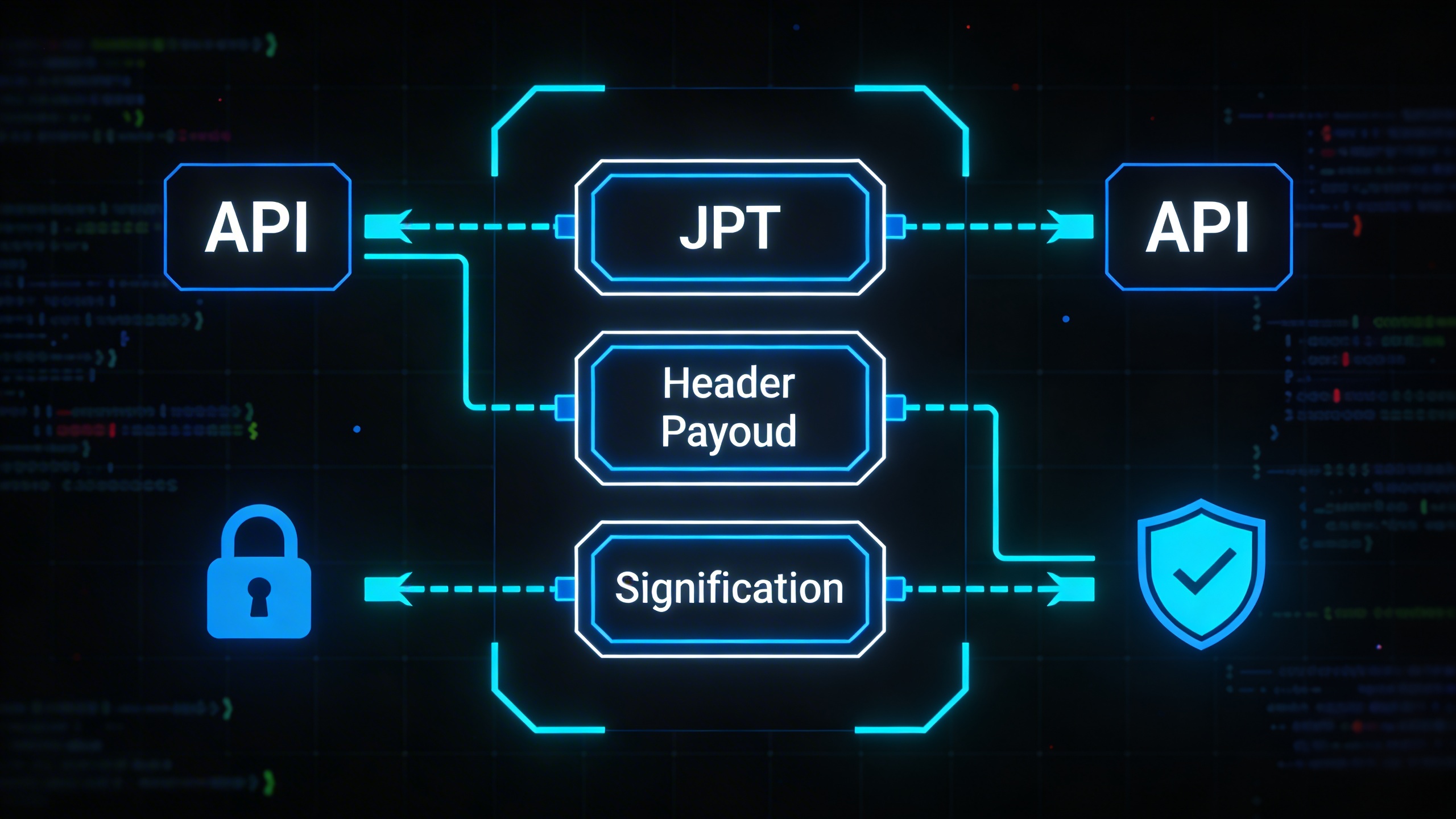
The Three Pillars: Understanding JWT Structure
A JWT is essentially a long string of characters, but it's not just a random jumble. It's composed of three distinct parts, separated by dots (.):
header.payload.signature
Let's break down each component:
1. The Header
The header typically consists of two parts: the type of the token, which is JWT, and the signing algorithm being used, such as HMAC SHA256 or RSA. These algorithms determine how the token's signature will be created.
Here’s an example of a header:
{
"alg": "HS256",
"typ": "JWT"
}
alg: Specifies the algorithm used for signing the token.HS256means HMAC with SHA-256.typ: Indicates the type of the token, which isJWT.
This JSON object is then Base64Url encoded to form the first part of the JWT.
2. The Payload (Claims)
The payload contains the 'claims' – statements about an entity (usually the user) and additional data. Claims are key-value pairs that convey information. There are three types of claims:
-
Registered Claims: These are a set of predefined claims that are not mandatory but recommended to provide a set of useful, interoperable claims. Examples include:
iss(issuer): Identifies the principal that issued the JWT.sub(subject): Identifies the principal that is the subject of the JWT.aud(audience): Identifies the recipients that the JWT is intended for.exp(expiration time): Identifies the expiration time on or after which the JWT MUST NOT be accepted for processing.nbf(not before): Identifies the time before which the JWT MUST NOT be accepted for processing.iat(issued at): Identifies the time at which the JWT was issued.jti(JWT ID): Provides a unique identifier for the JWT.
-
Public Claims: These can be defined by anyone using JWTs. They should be registered in the IANA JSON Web Token Registry or be defined as a URI that contains a collision-resistant name. This prevents collisions when using custom claim names.
-
Private Claims: These are custom claims created to share information between parties that agree on their meaning. They are not registered and should be used with caution to avoid collisions.
Example payload:
{
"sub": "1234567890",
"name": "John Doe",
"admin": true,
"iat": 1516239022,
"exp": 1516242622
}
Similar to the header, this JSON object is also Base64Url encoded to form the second part of the JWT.
3. The Signature
The signature is the most crucial part for ensuring the integrity and authenticity of the token. It's created by taking the Base64Url encoded header, the Base64Url encoded payload, a secret (a string known only to the issuer and the verifier), and applying the algorithm specified in the header.
The signature is calculated as follows:
HMACSHA256( Base64UrlEncode(header) + "." + Base64UrlEncode(payload), secret)
- Integrity: If the token's header or payload is tampered with by an unauthorized party, the signature will no longer match, and the token will be considered invalid. This prevents attackers from altering the claims (e.g., changing
"admin": falseto"admin": true). - Authenticity: Only someone with the secret key can generate a valid signature. This ensures that the token was indeed issued by a trusted entity.
Once all three parts are generated and encoded, they are concatenated with dots to form the complete JWT string.
Want to inspect a JWT and see its parts decoded in real-time? Check out the JWT Decoder on DevToolHere.com. It's an invaluable tool for understanding the structure and content of any JWT you encounter.
How JWTs Work: The Authentication Flow
Understanding the structure is one thing; seeing how JWTs fit into a typical authentication and authorization flow is another. Here's a common scenario:
- User Authentication (Login): A user provides their credentials (e.g., username and password) to the authentication server.
- Credential Verification: The server verifies these credentials (e.g., by checking against a database).
- Token Issuance: If the credentials are valid, the server creates a JWT. This JWT contains claims about the user (e.g., user ID, roles, expiration time) and signs it with a secret key.
- Token Transmission: The server sends the signed JWT back to the client (e.g., browser, mobile app) as part of the response.
- Client Storage: The client typically stores this JWT (e.g., in
localStorage,sessionStorage, or an HTTP-only cookie). - Subsequent Requests: For every subsequent request to protected routes or resources, the client includes the JWT, usually in the
Authorizationheader as aBearertoken (e.g.,Authorization: Bearer <token>). - Server-Side Validation: When the server receives a request with a JWT:
- It extracts the token from the header.
- It verifies the token's signature using the same secret key it used to sign it. If the signature is invalid, the token is rejected.
- It checks the token's claims, such as the expiration time (
exp) and any other relevant permissions.
- Access Granted/Denied: If the token is valid and the claims grant the necessary permissions, the server processes the request. Otherwise, it denies access.
This stateless approach means the server doesn't need to maintain session information for each logged-in user, which significantly simplifies scaling and distributed architectures.
Real-World Use Cases and Scenarios for JWTs
JWTs are incredibly versatile and find application in a wide array of scenarios:
1. Authentication and Authorization
This is the most common use case. After a user logs in, a JWT is issued, which the client then uses to prove their identity and access protected resources. This is particularly powerful for:
- Single Sign-On (SSO): A user logs in once to an identity provider, which issues a JWT. This token can then be used to access multiple services without re-authenticating.
- API Security: RESTful APIs often use JWTs for authenticating requests, ensuring that only authorized clients can access specific endpoints. This is especially prevalent in microservices architectures where services need to communicate securely without complex session management.
- Mobile Applications: Mobile apps can easily store and send JWTs with API requests, providing a seamless user experience.
2. Information Exchange
JWTs can securely transmit information between parties. Because the information is signed, you can be sure that the sender is who they claim to be and that the message hasn't been altered. This is useful for:
- Inter-service Communication: In a microservices environment, one service might issue a JWT containing specific data (e.g., a user's ID and permissions) to another service, trusting the data because of the signature.
- Securely Passing Data: For example, a payment gateway might issue a JWT to a merchant containing transaction details that the merchant can then use to update their records, confident in the data's integrity.
3. Stateless Sessions
Traditional web applications often rely on server-side sessions, storing user data on the server and using a session ID in cookies. JWTs enable stateless sessions where all necessary user data is contained within the token itself. This is beneficial for:
- Scalability: Any server can validate the token without needing to access a centralized session store, making it easier to scale horizontally.
- Load Balancing: Requests can be routed to any server in a cluster without session affinity, simplifying load balancing.
The Advantages of Embracing JWTs
JWTs offer several compelling benefits that make them a preferred choice for modern applications:
- Statelessness: Servers don't need to store session data. This simplifies horizontal scaling, as any server can process any request without needing to fetch session details from a shared store.
- Compactness: JWTs are smaller than XML-based security tokens like SAML, making them efficient for transmission, especially over HTTP headers.
- Self-Contained: All necessary information about the user and their permissions is within the token, reducing the need for database lookups on every request.
- Decentralization: Different services can issue and validate tokens independently, as long as they share the same secret key (for symmetric algorithms) or public/private key pair (for asymmetric algorithms).
- Mobile-Friendly: Easy to implement in mobile applications, as tokens can be stored securely and sent with each API request.
- Interoperability: Being an open standard, JWTs are supported by a wide range of programming languages and platforms.
Potential Downsides and Crucial Considerations
While powerful, JWTs are not a silver bullet. It's important to be aware of their limitations and how to mitigate them.
1. Token Revocation
One of the biggest challenges with JWTs is revocation. Since JWTs are stateless and self-contained, once issued, they are typically valid until their expiration time. This makes immediate revocation (e.g., for logout, password change, or compromised account) difficult without introducing server-side state.
Mitigation Strategies:
- Short Expiration Times: Use short-lived access tokens (e.g., 5-15 minutes) to minimize the window of vulnerability.
- Refresh Tokens: Pair short-lived access tokens with long-lived refresh tokens. When an access token expires, the client uses the refresh token to obtain a new access token. Refresh tokens can be stored on the server and revoked if necessary, reintroducing some state but only for refresh operations, not every API call.
- Blacklisting/Denylist: Maintain a server-side denylist of revoked JWTs. For every incoming JWT, check if it's on the denylist. This reintroduces state and requires a fast lookup mechanism (e.g., Redis), but it allows for immediate revocation.
2. Token Size
While generally compact, if you stuff too many claims into the payload, the JWT can become large. Since it's often sent in the Authorization header, a very large token can add overhead to every request, potentially impacting performance.
Mitigation: Only include essential claims in the JWT. For less frequently needed data, perform a database lookup or use a separate API endpoint.
3. Security Best Practices are Paramount
JWTs are secure if implemented correctly. Misconfigurations can lead to significant vulnerabilities.
Implementing JWTs: A Practical Example (Node.js)
Let's look at a basic example of how to generate and verify JWTs using Node.js with the popular jsonwebtoken library.
First, install the library:
npm install jsonwebtoken
Generating a JWT
const jwt = require('jsonwebtoken');
// A secret key (should be stored securely, e.g., in environment variables)
const SECRET_KEY = 'your_super_secret_key_here';
// Payload data (claims)
const payload = {
userId: 'user123',
username: 'johndoe',
roles: ['user'],
isAdmin: false
};
// Options for token signing
const options = {
expiresIn: '1h', // Token expires in 1 hour
issuer: 'devtoolhere.com' // Issuer of the token
};
// Sign the token
const token = jwt.sign(payload, SECRET_KEY, options);
console.log('Generated JWT:', token);
// Example output:
// eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VySWQiOiJ1c2VyMTIzIiwidXNlcm5hbWUiOiJqb2huZG9lIiwicm9sZXMiOlsidXNlciJdLCJpc0FkbWluIjpmYWxzZSwiaWF0IjoxNjQ4NjU2MDAwLCJleHAiOjE2NDg2NTk2MDAsImlzcyI6ImRldnRvb2xoZXJlLmNvbSJ9.SomeRandomSignaturePart
Verifying a JWT
const jwt = require('jsonwebtoken');
const SECRET_KEY = 'your_super_secret_key_here'; // Must be the same secret used for signing
const receivedToken = 'eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VySWQiOiJ1c2VyMTIzIiwidXNlcm5hbWUiOiJqb2huZG9lIiwicm9sZXMiOlsidXNlciJdLCJpc0FkbWluIjpmYWxzZSwiaWF0IjoxNjQ4NjU2MDAwLCJleHAiOjE2NDg2NTk2MDAsImlzcyI6ImRldnRvb2xoZXJlLmNvbSJ9.SomeRandomSignaturePart'; // Replace with an actual generated token
try {
const decoded = jwt.verify(receivedToken, SECRET_KEY);
console.log('Decoded JWT:', decoded);
// Output:
// {
// userId: 'user123',
// username: 'johndoe',
// roles: [ 'user' ],
// isAdmin: false,
// iat: 1648656000,
// exp: 1648659600,
// iss: 'devtoolhere.com'
// }
} catch (err) {
console.error('JWT Verification Failed:', err.message);
// Common errors: 'invalid signature', 'jwt expired', 'jwt malformed'
}
As you can see, the jwt.verify method handles the signature validation and expiration checks automatically. If you want to quickly inspect the contents of a JWT without writing code, remember to use our JWT Decoder tool.
Essential Security Best Practices for JWT Implementation
Implementing JWTs effectively requires adherence to strict security practices:
-
Use Strong, Unique Secrets: The
SECRET_KEYused to sign your tokens must be long, complex, and kept absolutely confidential. Never hardcode it in your application; use environment variables or a secure key management system. For production, consider using asymmetric (RSA, ECDSA) algorithms where a private key signs the token and a public key verifies it, offering better key management. -
Set Appropriate Expiration Times (
expclaim): Short-lived access tokens are crucial. If an access token is compromised, the damage window is limited. Combine them with refresh tokens for a better user experience. -
Secure Token Storage on the Client-Side:
- HTTP-Only Cookies: For web applications, storing JWTs in HTTP-only cookies can mitigate XSS (Cross-Site Scripting) attacks, as JavaScript cannot access them. However, they are vulnerable to CSRF (Cross-Site Request Forgery) attacks, which can be mitigated with anti-CSRF tokens or
SameSite=Strictpolicies. - Local Storage/Session Storage: While accessible via JavaScript, making them convenient, they are highly susceptible to XSS attacks. If an attacker injects malicious script, they can steal the token. If you must use them, ensure robust XSS protection (Content Security Policy, proper input sanitization).
- Memory (for SPAs): Store tokens in memory and clear them on page refresh or tab close, forcing re-authentication. This is the most secure against persistent XSS but impacts UX.
- Mobile Apps: Use secure storage mechanisms provided by the OS (e.g., iOS Keychain, Android Keystore).
- HTTP-Only Cookies: For web applications, storing JWTs in HTTP-only cookies can mitigate XSS (Cross-Site Scripting) attacks, as JavaScript cannot access them. However, they are vulnerable to CSRF (Cross-Site Request Forgery) attacks, which can be mitigated with anti-CSRF tokens or
-
Always Use HTTPS: Ensure all communication between the client and server is encrypted using HTTPS. This prevents man-in-the-middle attacks from intercepting and stealing JWTs.
-
Validate All Claims: Beyond just signature verification, always validate the registered claims like
iss(issuer),aud(audience), andnbf(not before) to ensure the token is intended for your application and is within its valid time frame. -
Implement Refresh Tokens Correctly: Refresh tokens should be long-lived, stored securely (e.g., in an HTTP-only cookie, or a secure database for server-side validation), and used only once to obtain new access tokens. They should also be revocable.
-
Consider Token Revocation: For critical applications, implement a denylist/blacklist system for immediate revocation of compromised tokens or for forced logouts. This reintroduces some state but is necessary for high-security scenarios.
-
Avoid Storing Sensitive Data in the Payload: While JWTs are signed, the payload is only Base64Url encoded, not encrypted. Anyone can decode it and read its contents. Never put sensitive personal identifiable information (PII) or secrets in the payload. Only include necessary, non-sensitive claims.
Beyond JWTs: Related Concepts
JWTs often work in conjunction with other protocols and standards:
- OAuth 2.0: OAuth 2.0 is an authorization framework, not an authentication protocol. It delegates user authentication to an authorization service and issues access tokens (which can be JWTs) to client applications. JWTs are commonly used as the format for these access tokens.
- OpenID Connect (OIDC): OIDC is an authentication layer built on top of OAuth 2.0. It defines a standard way for clients to verify the identity of the end-user based on the authentication performed by an authorization server, as well as to obtain basic profile information about the end-user. OIDC uses JWTs (specifically, ID Tokens) to carry user identity information.
Understanding these relationships helps position JWTs within the broader ecosystem of modern identity and access management.
Conclusion and Key Takeaways
JSON Web Tokens have revolutionized how we approach authentication and authorization in distributed systems. Their stateless, self-contained nature offers significant advantages in scalability, performance, and simplicity, making them a cornerstone technology for modern web and mobile applications, microservices, and APIs.
However, the power of JWTs comes with a responsibility. Proper implementation, rigorous adherence to security best practices, and a clear understanding of their limitations are paramount to harnessing their benefits without introducing vulnerabilities. From choosing strong secrets and setting appropriate expiration times to securely storing tokens and implementing robust revocation strategies, every detail matters.
By following the guidelines outlined in this guide, you are well-equipped to integrate JWTs securely and efficiently into your development workflow, building more robust and scalable applications. And remember, for quick inspections and debugging of your tokens, the JWT Decoder on DevToolHere.com is always at your fingertips.
Happy coding, and stay secure!